CrowdStrike is a cloud-based next-generation antivirus, EDR (endpoint detection and response) solution. You can deploy CrowdStrike in your infrastructure via a single lightweight agent. In this post, we will discuss how we can install CrowdStrike falcon agent / Sensor using Intune on Azure AD joined devices.
Step 1: Download the CrowdStrike agent
Login to CrowdStrike Portal and download the agent. You can find step-by-step instructions in the below article:
https://www.crowdstrike.com/blog/tech-center/install-falcon-sensor/
Step 2: Create the Install.cmd file
Once you have downloaded the agent, copy it in a folder and create a file Install.cmd.
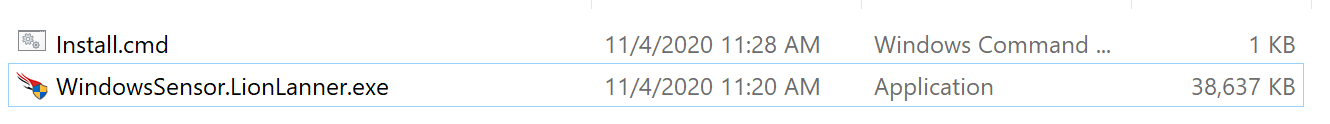
Use the following code in Install.cmd. You should use your own CID (Customer ID):
@ECHO OFF
SET ThisScriptsDirectory=%~dp0
WindowsSensor.LionLanner.exe /install /quiet /norestart CID=02A1C79U38044E2XXXXXXX-FA
CrowdStrike Falcon Agent Install Switches
| Switch | Description |
|---|---|
| CID= | Customer ID Checksum, which is required when installing. |
| MAINTENANCE_TOKEN= | Bulk Maintenance Token is retrieved from the CrowdStrike site when performing upgrades. |
| /install | Install the sensor (default). |
| /passive | The installer shows a minimal UI with no prompts. |
| /quiet | The installer shows no UI and no prompts. |
| /norestart | Prevents the host from restarting at the end of the sensor installation. |
Step 3: Create the Intune package
Now create an Intune package using Intune Packaging App. (Change source path and destination folder path)
PS C:\IntuneAppsWinAppsUtil> .\IntuneWinAppUtil.exe
Please specify the source folder: C:\CrowdStrike
Please specify the setup file: Install.cmd
Please specify the output folder: C:\CrowdStrike
Do you want to specify catalog folder (Y/N)? N
Step 4: Add the app in Intune
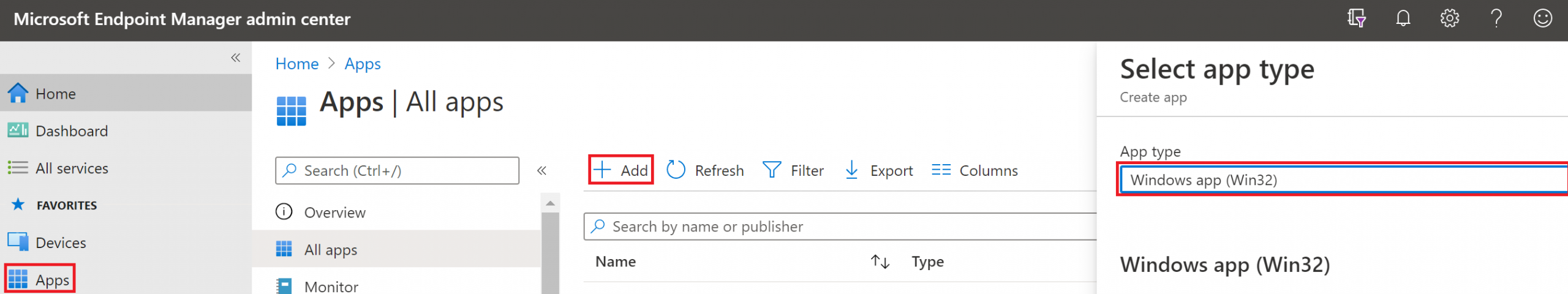
Login to https://endpoint.Microsoft.com and Select Apps.
Select all Apps and Click to Add. Select App Type to "Windows app (Win32)".
Step 5: Upload the package file
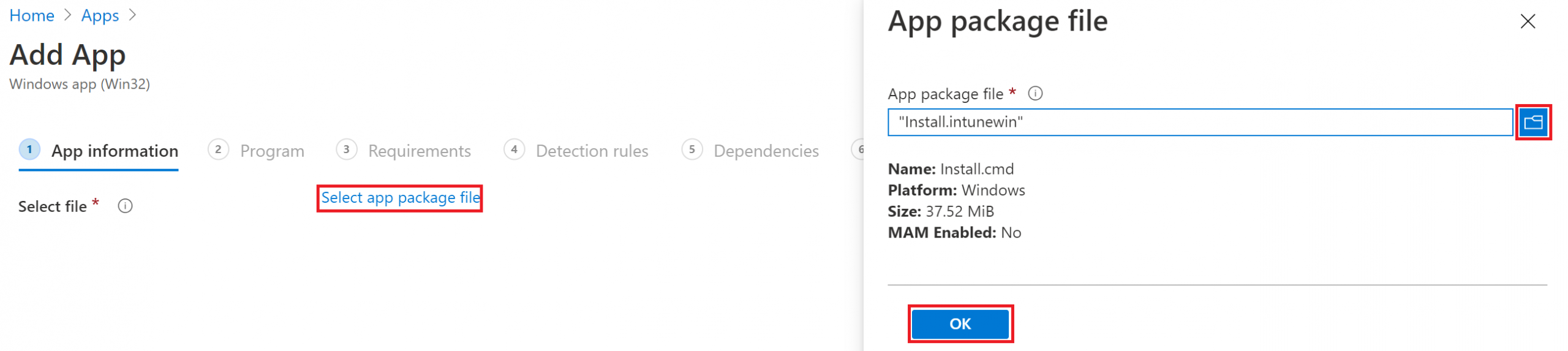
Select App Package file which we created earlier.
Step 6: Configure app information
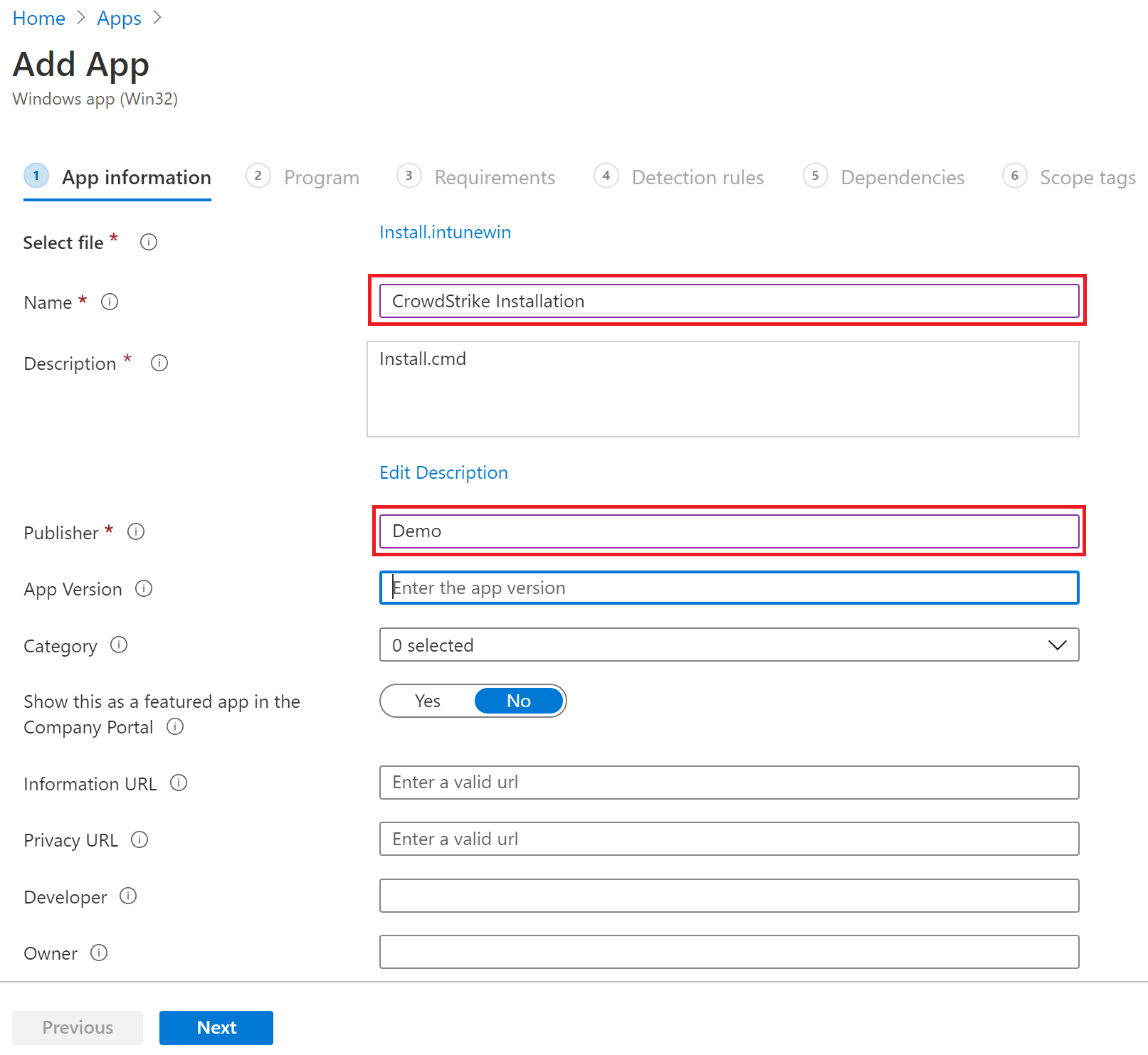
Add app information such as Name & Publisher.
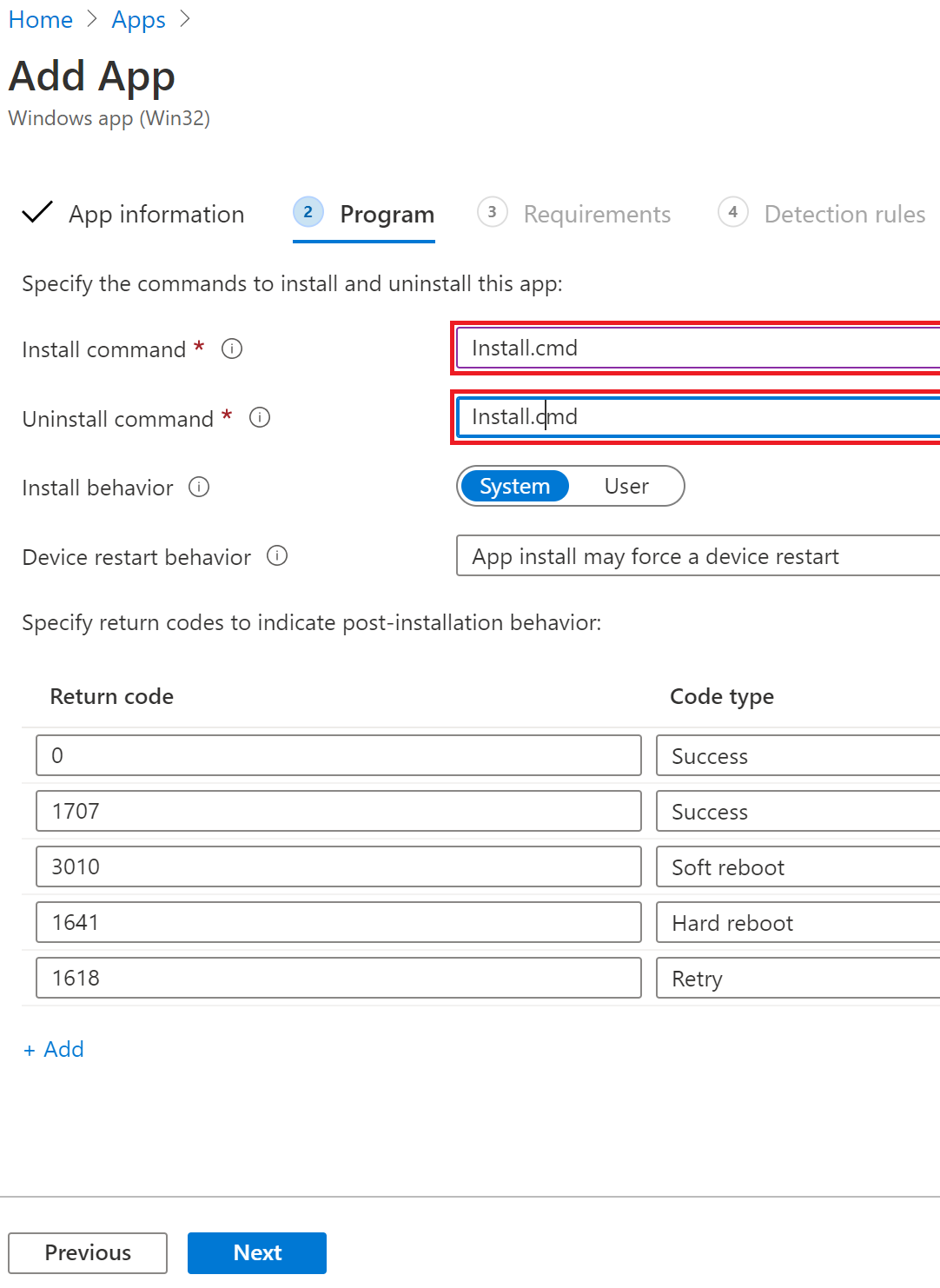
Step 7: Set install and uninstall commands
Specify the commands to install and uninstall this app.
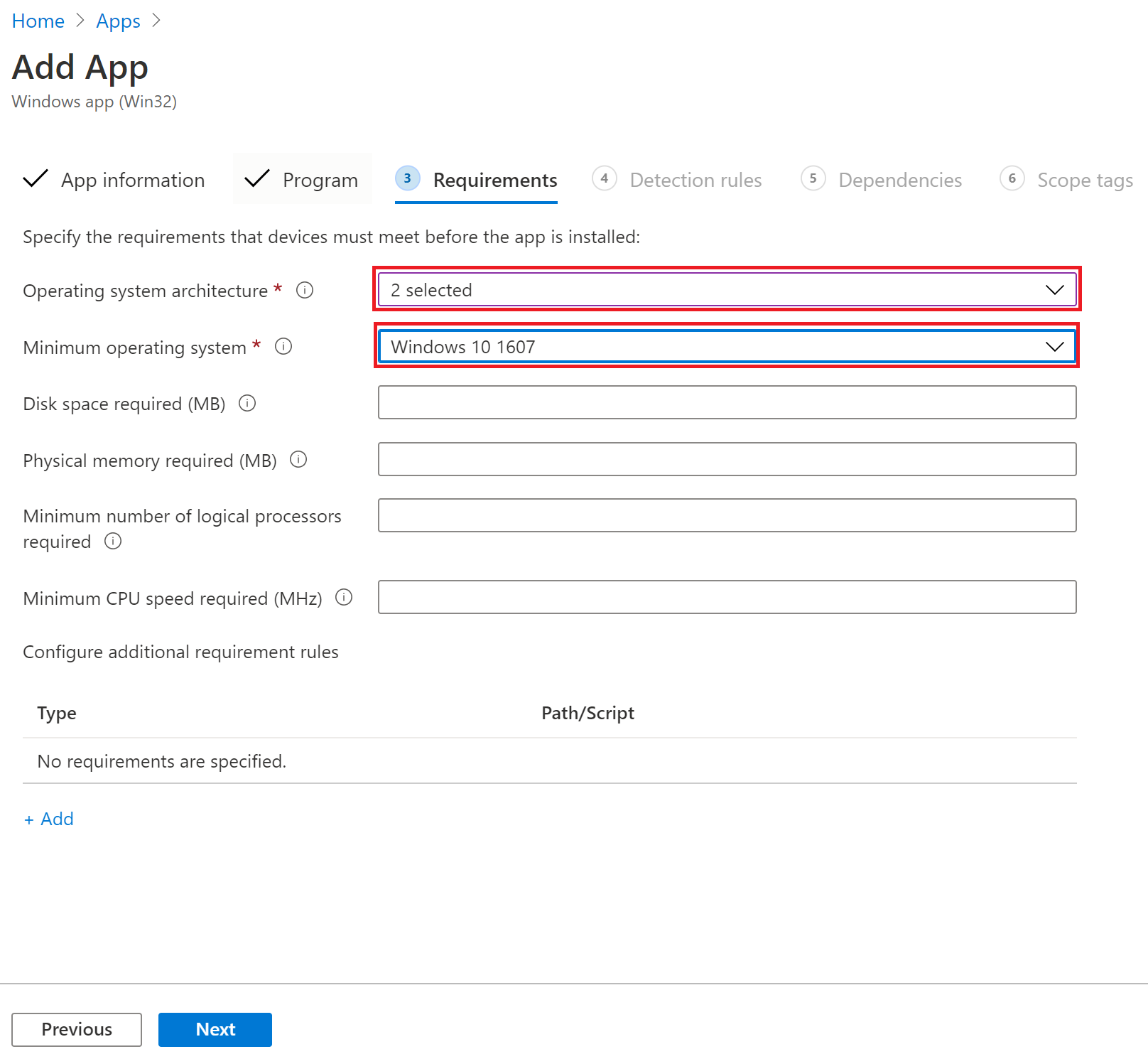
Step 8: Configure requirements
Select both OS system architecture and minimum OS to Windows 10 1607.
Step 9: Set detection rules
On detection rule, select "Manually configure detection rules and Rule type Register".
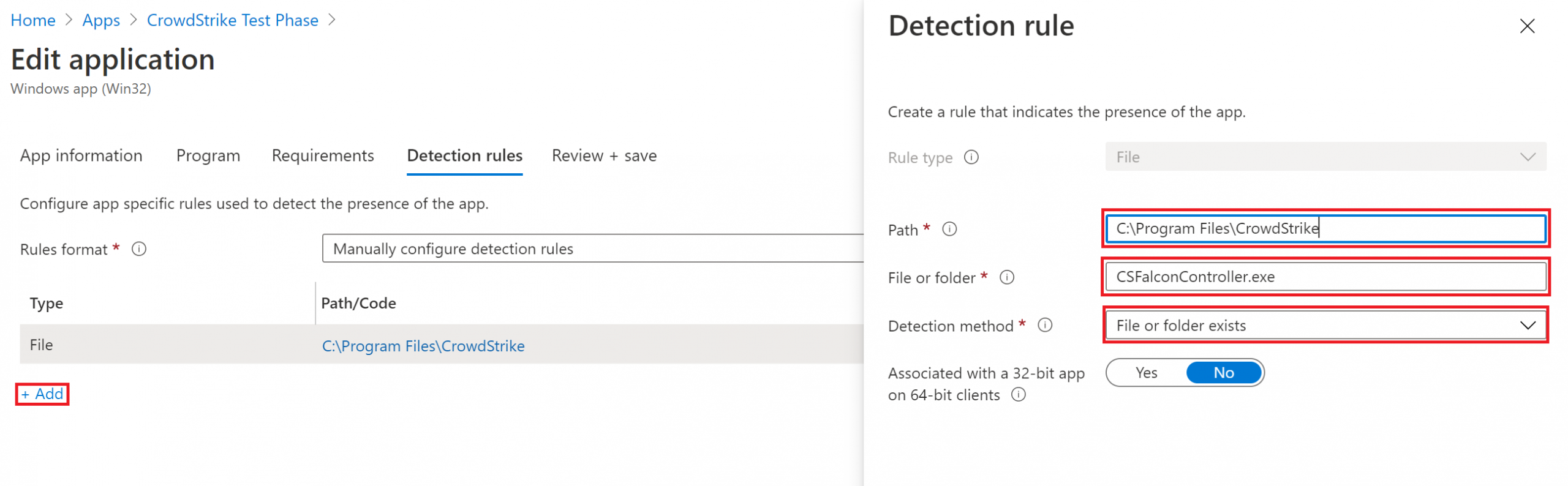
Path: C:\Program Files\CrowdStrike
File or folder: CSFalconController.exe
Step 10: Assign to a group
Assign to the group you want to deploy CrowdStrike using Intune.