Microsoft Graph is a powerful API that allows developers to interact with various Microsoft 365 services, such as Entra ID (Azure Active Directory), Exchange Online, SharePoint, and more. In this blog post, we will explore how to connect to Microsoft Graph using PowerShell, highlighting the differences from the Entra ID (Azure AD) PowerShell module and demonstrating the unique features of Microsoft Graph.
Prerequisites
Before we dive in, make sure you have the following prerequisites:
- PowerShell Installed: Ensure that you have PowerShell installed on your machine. If not, download and install the latest version from the official PowerShell website.
- Registered Application in Azure AD: To interact with Microsoft Graph, you need to register an application in Entra ID(Azure AD). Follow the steps in the Azure portal to register your application and note down the Application (client) ID and Directory (tenant) ID.
- API Permissions: Make sure your application has the necessary permissions to access Microsoft Graph. Configure these permissions in the Azure portal.
How it Differs from Azure AD PowerShell Module
The Azure AD PowerShell module primarily focuses on managing Azure Active Directory, offering cmdlets for tasks like managing users, groups, and roles within Entra ID (Azure AD). On the other hand, the Microsoft Graph PowerShell module extends the capabilities to interact with various Microsoft 365 services beyond Entra ID (Azure AD).
Unified Endpoint
One key difference is that Microsoft Graph uses a unified endpoint for accessing multiple services, providing a more holistic approach compared to the Entra ID (Azure AD) module, which is more focused on directory-related tasks.
Richer Set of Capabilities
Microsoft Graph PowerShell module offers a broader range of functionalities, allowing you to work with resources such as emails, files, calendars, and more across the entire Microsoft 365 suite.
Modern Authentication
Microsoft Graph PowerShell module leverages modern authentication, making it more aligned with current security best practices. It supports OAuth 2.0 authentication, including device code flow, making the authentication process more user-friendly.
Registered Application in Entra ID (Azure AD)
Step 1: Sign in to the Azure portal
- Navigate to the Azure portal.
- Sign in with an account that has the necessary permissions to register applications in the target Azure AD.
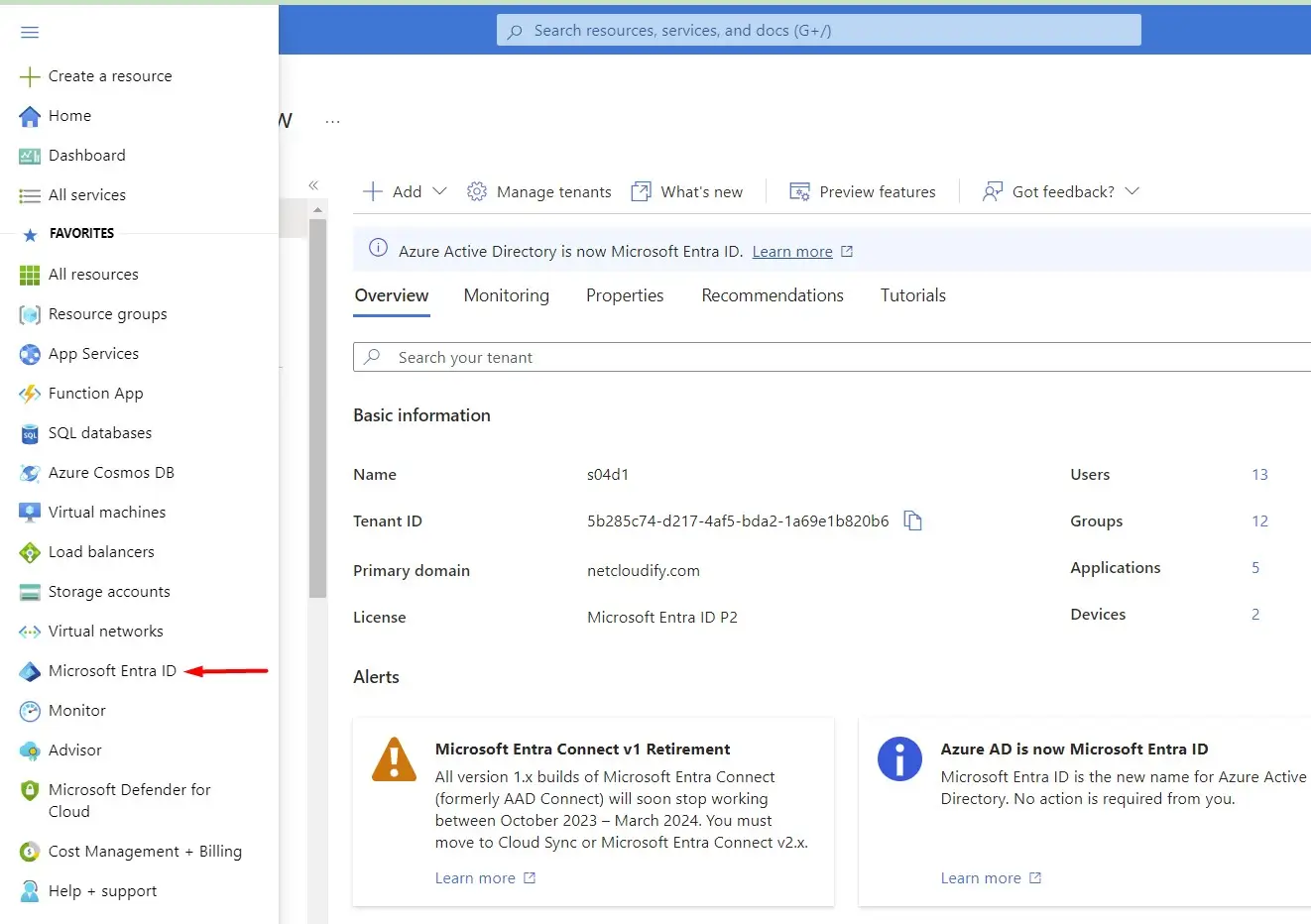
Step 2: Open the Microsoft Entra AD service
- In the left sidebar, click on "Microsoft Entra ID (Azure Active Directory)."
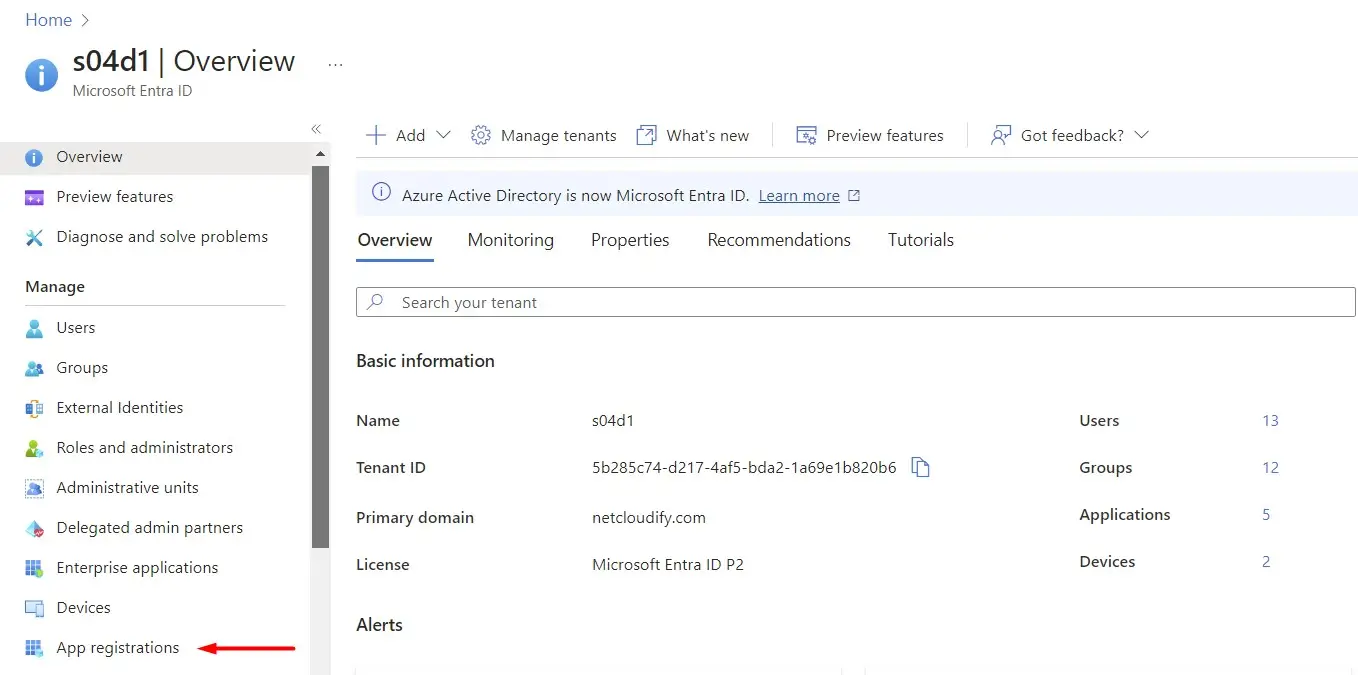
Step 3: Access the "App registrations" section
- Under the "Manage" section, click on "App registrations."
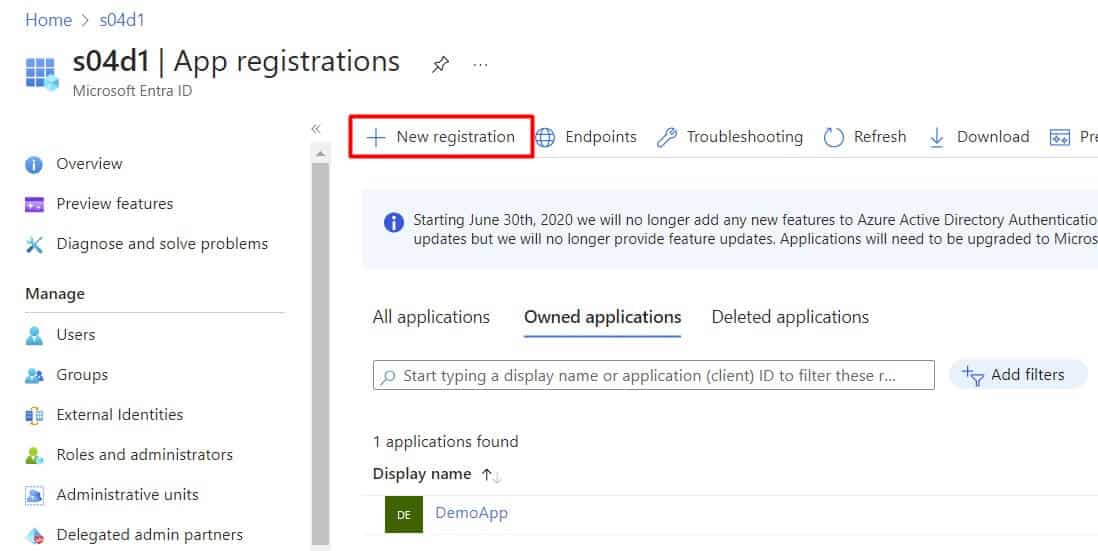
Step 4: Register a new application
- Click on the "New registration" button at the top.
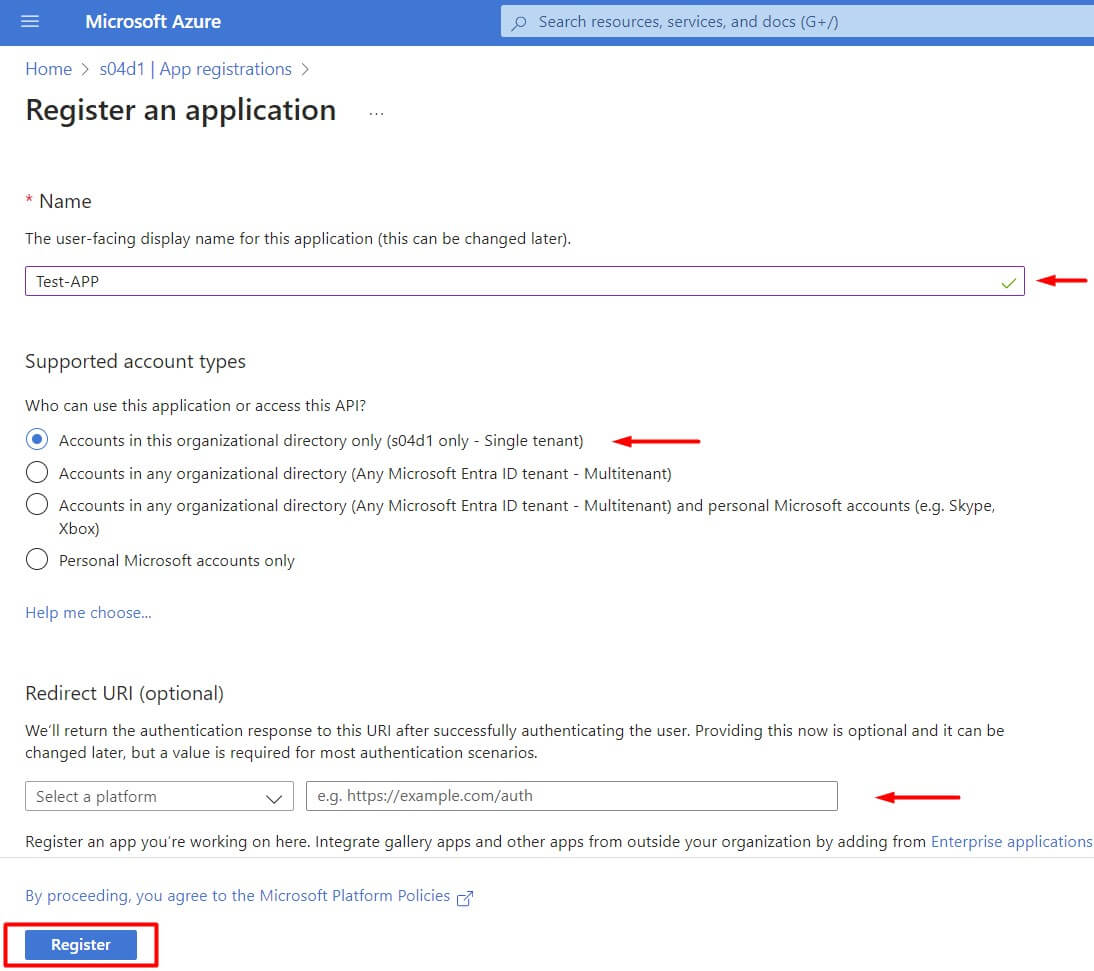
- Fill in the required information on the "Register an application" page:
- Name: Enter a meaningful name for your application.
- Supported account types: Choose the appropriate option based on your use case (e.g., "Accounts in this organizational directory only").
- In the "Redirect URI (optional)" section:
- If your application requires a redirect URI (e.g., for OAuth 2.0 authorization code flow), enter the appropriate URI. For testing purposes, you can use
http://localhost.
- If your application requires a redirect URI (e.g., for OAuth 2.0 authorization code flow), enter the appropriate URI. For testing purposes, you can use
- Click the "Register" button.
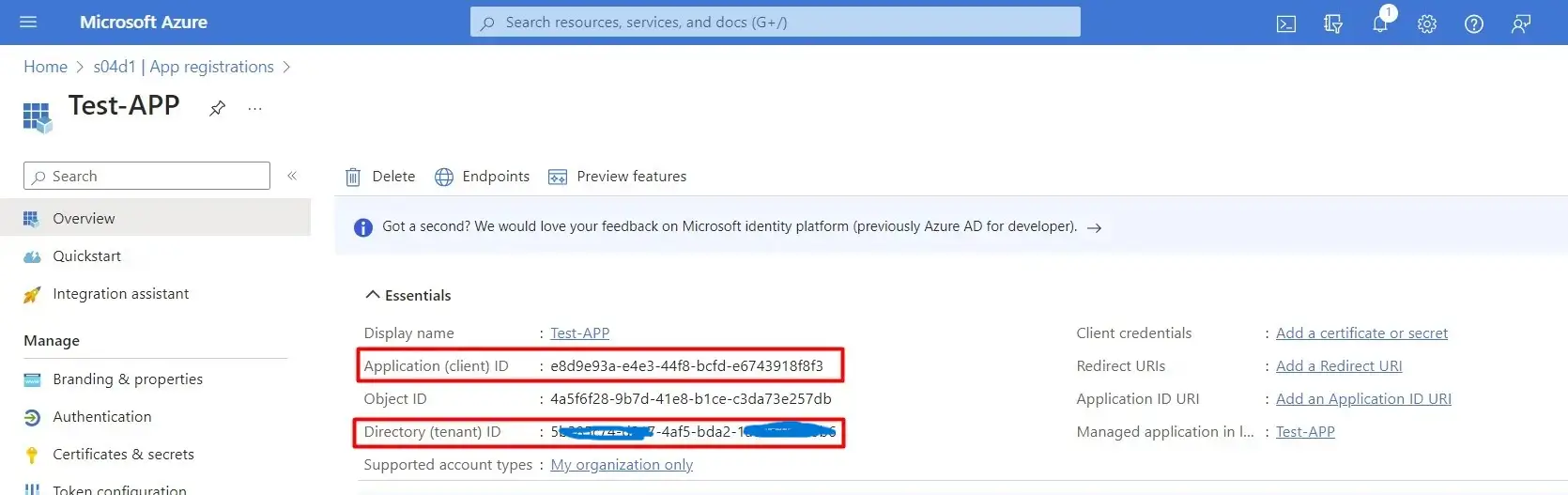
Step 5: Note down the Application (client) ID and Directory (tenant) ID
- After registration, you will be redirected to the overview page of your newly registered application.
- Note down the "Application (client) ID" and "Directory (tenant) ID." You will need these values for authentication.
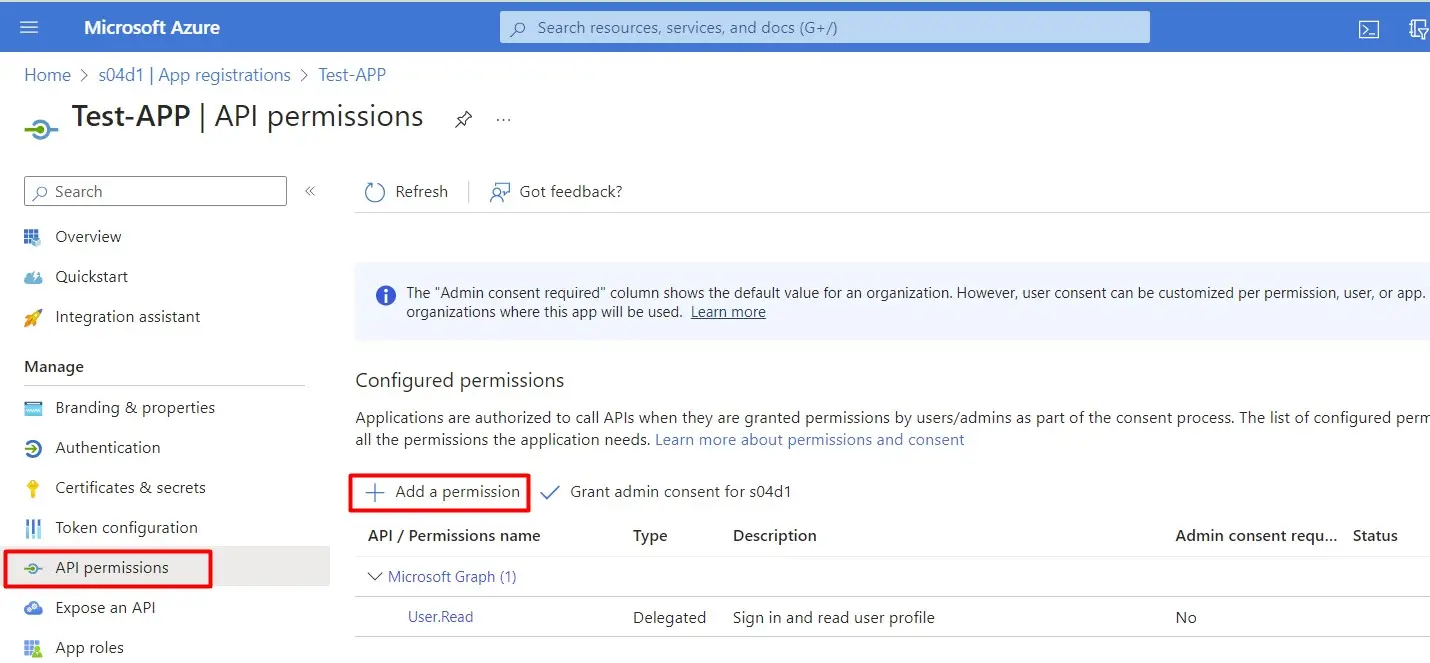
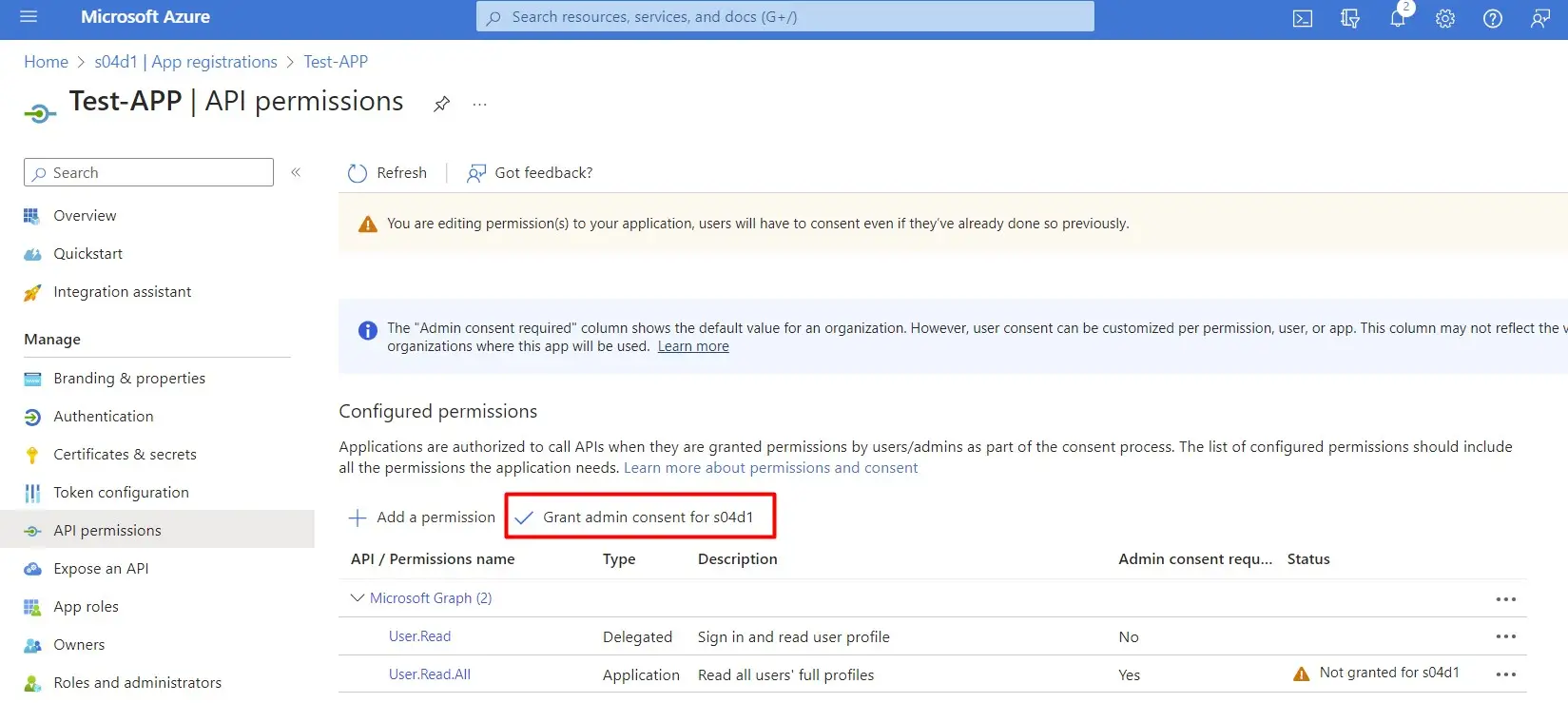
Step 6: Configure API permissions
- In the left sidebar, click on "API permissions."
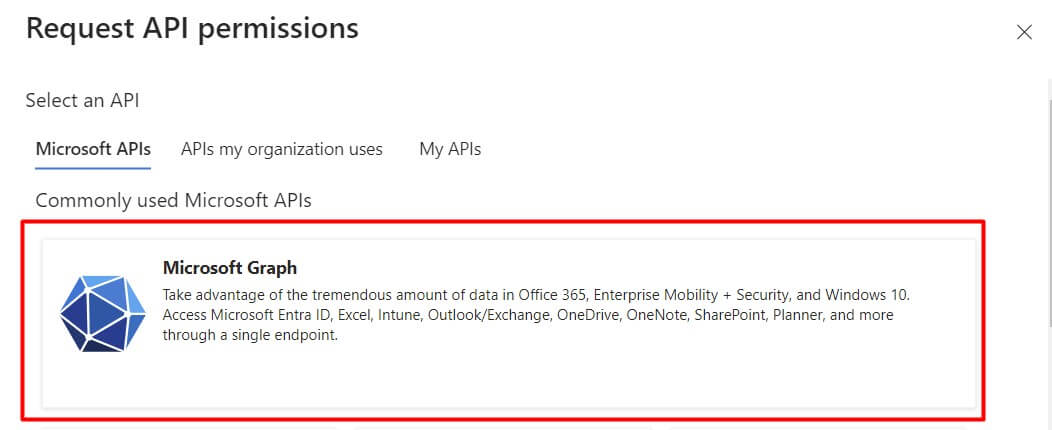
- Click on "Add a permission," then select the Microsoft Graph API.
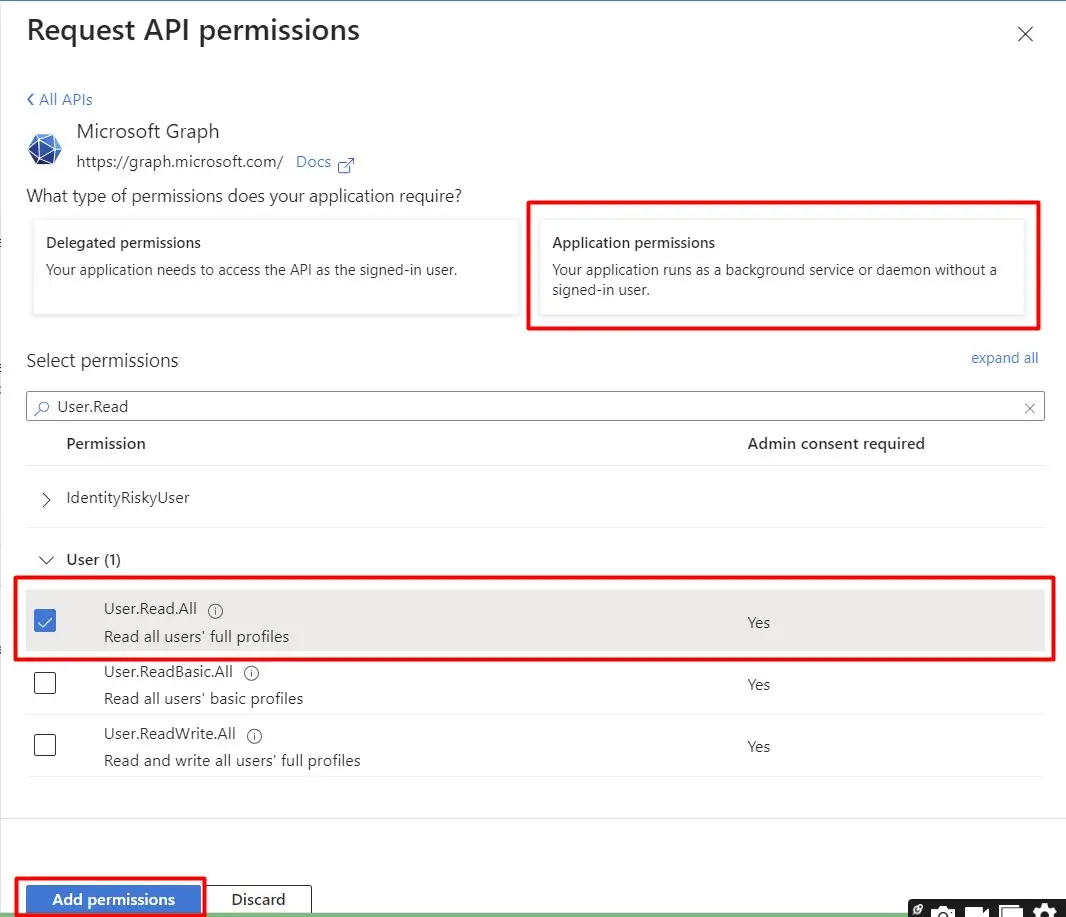
- Choose the necessary permissions required for your application (e.g.,
User.Read,Mail.Read, etc.). Click "Add permissions." - Don't forget to click on "Grant admin consent for [your organization]" to ensure the required permissions are granted.
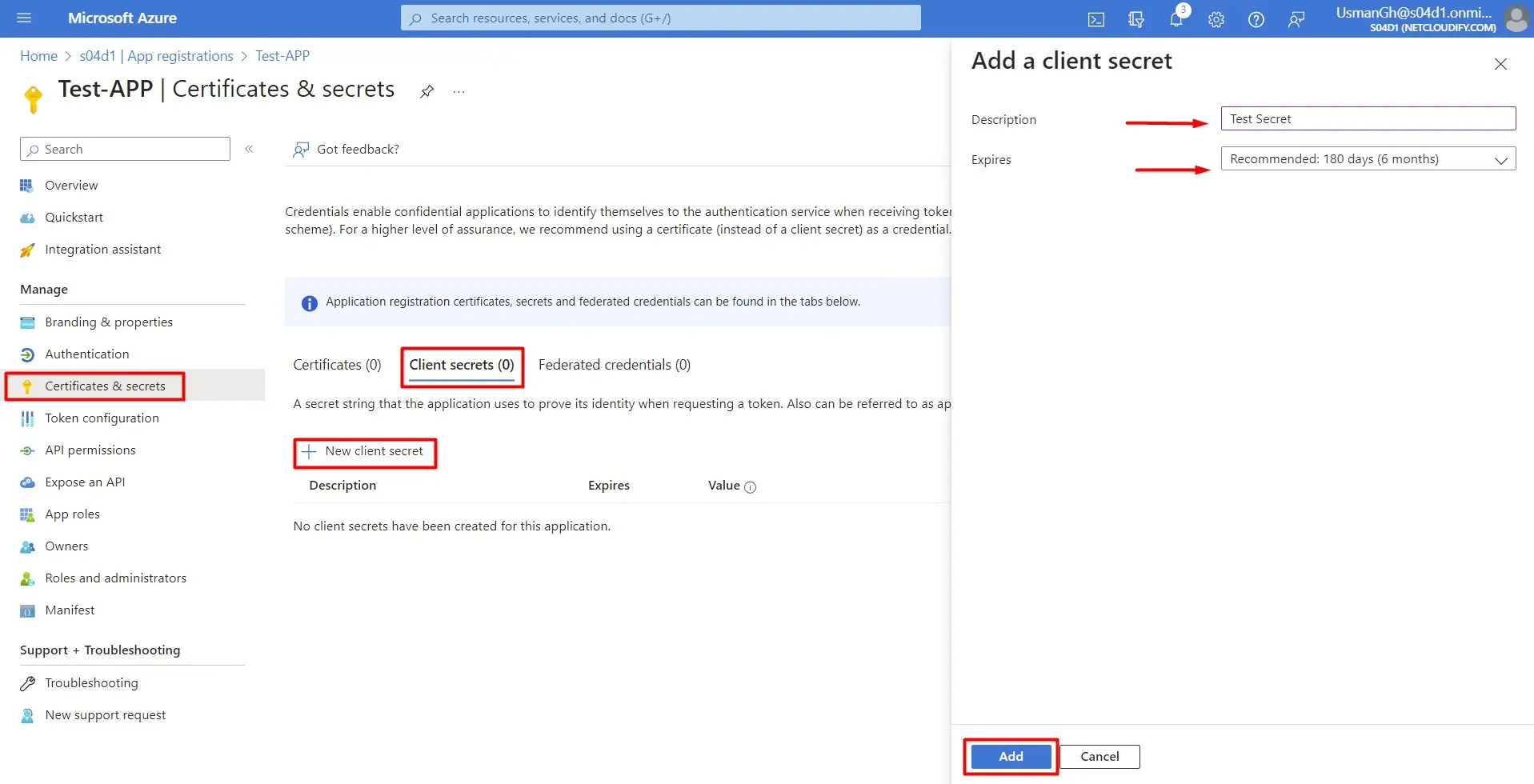
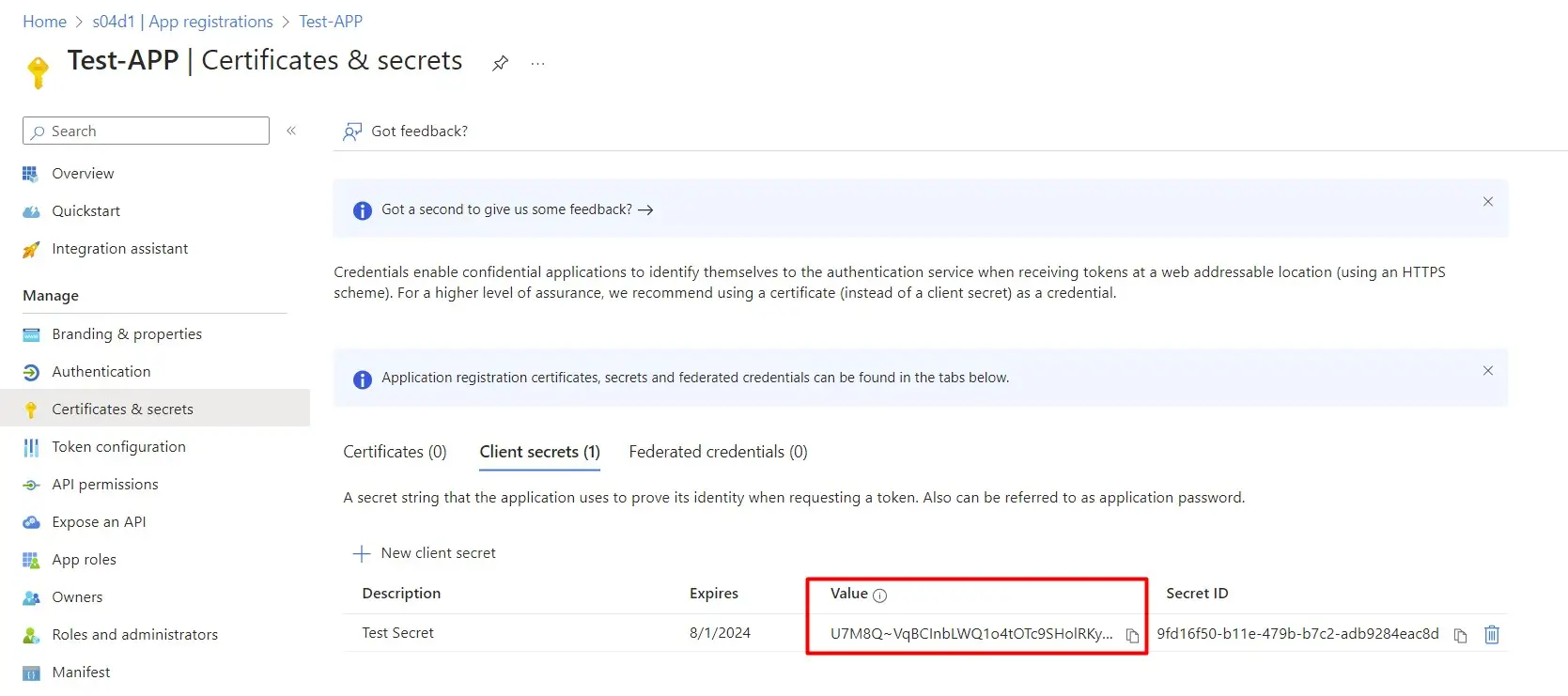
Step 7: Generate client secret (optional, based on your authentication method)
- In the left sidebar, click on "Certificates & secrets."
- Under the "Client secrets" section, click on "New client secret."
- Enter a description and choose an expiration period.
- Note down the value of the generated client secret. This secret is required for certain authentication flows.
Connecting to Microsoft Graph Using PowerShell
Step 1: Install the required modules
Open PowerShell as an administrator and install the required modules:
Install-Module -Name Microsoft.Graph
Install-Module -Name Microsoft.Graph.Authentication
Step 2: Authenticate with Azure AD
Use the following script to authenticate with Entra ID (Azure AD) using your registered application credentials:
# Replace these values with your application and directory IDs
$clientId = "your-application-id"
$tenantId = "your-directory-id"
$redirectUri = "http://localhost"
$clientSecret = "your-client-secret"
# Authenticate and obtain a token
$token = Get-MgAccessToken -ClientId $clientId -TenantId $tenantId -ClientSecret $clientSecret -RedirectUri $redirectUri
This script prompts you to log in and consent to the required permissions.
Step 3: Connect to Microsoft Graph
Now that you have obtained an access token, you can use it to connect to Microsoft Graph:
Connect-MgGraph -AccessToken $token.AccessToken
Congratulations! You are now connected to Microsoft Graph using PowerShell.
Example: Retrieve User Information
As a quick example, let's retrieve information about the signed-in user:
# Get user information
$user = Get-MgUser
Write-Host "User Display Name: $($user.DisplayName)"
Write-Host "User Principal Name: $($user.UserPrincipalName)"
This script fetches information about the signed-in user and displays their display name and user principal name, showcasing the interoperability of Microsoft Graph across Microsoft 365 services.
Connecting to Microsoft Graph using PowerShell provides a more extensive and integrated approach to managing Microsoft 365 services compared to the Azure AD PowerShell module. While the Azure AD module remains essential for directory-centric tasks, the Microsoft Graph module empowers you to interact with a broader spectrum of services using a unified endpoint.
Explore the capabilities of both modules and choose the one that best suits your specific requirements. Happy scripting!
Note: Azure AD PowerShell module is going to be depreciated soon.